- Why Us?
- Features
White Label
For SaaS Platforms & Agencies
Provide our complete analytics suite to your clients, directly within your own interface and with your/their own branding. Discover Analytics-as-a-Service and White Label Analytics. Great benefit, minimal effort.
- Pricing
- White Label
- Success Stories
- Partner
- ResourcesExpand Your Knowledge
Are your Website Integrations Privacy-Compliant?
A GDPR and ePrivacy checklist for third-party tools and non-essential services
- About this Checklist
- Review Storage and Client-Side Identifiers
- Assess Fingerprinting and Visitor Identification
- Verify Consent Handling and Legal Basis
- Inspect Data Transmission and Hosting Location
- Evaluate Data Minimization and Purpose Limitation
- Confirm Data Retention and Deletion Practices
- Validate Data Subject Rights and Access Controls
- Check Data Processing Agreement and Roles
- Confirm Transparency and Verifiability
- Review Accountability and Ongoing Compliance
Disclaimer: This checklist is provided for informational and technical verification purposes only and does not constitute legal advice. It helps assess the observable behavior of third-party tools against GDPR and ePrivacy requirements in practice. Compliance obligations, regulatory interpretation, and enforcement may vary by jurisdiction, and responsibility for compliance remains with the website operator. Where appropriate, independent legal advice should be sought.
Website operators often rely on third-party tools and non-essential services that are not strictly necessary for core site operation, such as analytics, optimization, personalization, or marketing tools. While these services frequently claim GDPR and ePrivacy compliance, this is rarely explained in practical or verifiable terms.
In practice, compliance depends on how they behave when embedded in a website, including:
- What data is collected
- How visitor consent is handled
- Where data is processed geographically
GDPR and the ePrivacy Directive represent the most comprehensive regulatory standards for website tools. An integration that can be verified as compliant under this framework will typically meet or exceed the requirements of other data protection regimes, subject to jurisdiction-specific obligations and interpretation.
About this Checklist
The page that follows provides a structured approach for assessing whether non-essential third-party services operating in a visitor’s browser meet the requirements of the GDPR and the ePrivacy Directive. It focuses on observable technical behavior and incorporates relevant case law and international data transfer considerations, rather than relying on stated claims.
Any references to third-party tools or examples are intended to illustrate verification methods, not endorsements, and the same steps should be applied to all tools under evaluation.
This checklist is intended to support practical compliance verification. Legal obligations and regulatory interpretation may vary depending on organizational role, jurisdiction, and specific use case. Organizations should assess applicable legal requirements and, where appropriate, seek independent legal advice when applying this framework to their own circumstances.
Review Storage and Client-Side Identifiers
Storage at the device level determines whether consent is required and whether data collection is lawful under GDPR and ePrivacy. This section examines how a third-party or non-essential service uses browser storage and client-side identifiers when embedded on a website.
Verification Guidance
When reviewing a service’s storage and client-side identifiers in your browser:
- Always test before consent and after consent
- Clear browser storage and reload between checks
- Focus on whether identifiers persist across sessions or page loads
- Test in both a privacy-restrictive browser and a Chromium-based browser
- Repeat checks in private or incognito mode
- Verify no unique identifiers appear in Cookies, Local Storage, or Session Storage
- Optionally review network requests for persistent identifiers
Compliance Checklist
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 1. | No cookies are set before consent is given. | ePrivacy Directive Art. 5(3); GDPR Art. 6(1) | Inspect browser cookies on first page load before interacting with any consent banner, and verify cookie ownership and purpose via documentation and configuration. | TWIPLA does not set cookies prior to consent. |
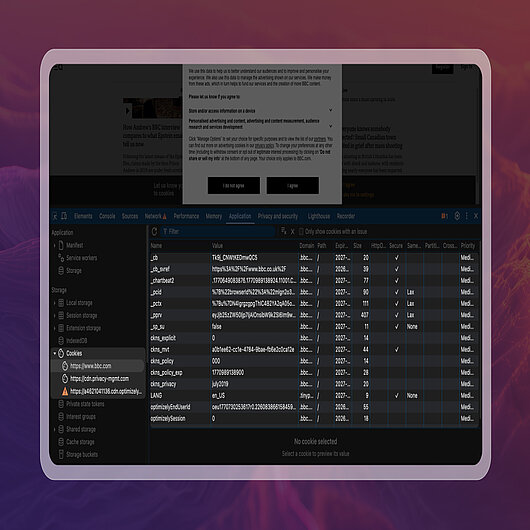
How this requirement is verified in practice:
- Browser path: right-click → Inspect → Application → Cookies.
- Load the website for the first time, keep the consent banner visible, and open the browser’s developer tools before interacting with the banner.
- The screenshot shows cookies present on initial page load prior to consent.
- To verify compliance for this requirement, review the listed cookies and confirm that none are used for tracking or visitor measurement.
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 2. | Any cookies in use are either technically necessary or require valid consent. | ePrivacy Directive Art. 5(3) ; GDPR Art. 6(1) | Review cookie purpose, scope, and lifespan using browser developer tools. Example: In Chrome DevTools → Application → Cookies, verify that no cookies associated with non-essential functionality are present prior to consent (for example, cookies used for tracking, measurement, personalization, or third-party services). Any cookies observed should be limited to essential site functionality, scoped to the first-party domain, and have a short or session-based lifespan. | TWIPLA does not use tracking or analytics cookies prior to consent, removing the need to classify cookies as technically necessary or consent-based. |
| 3. | Session Storage is used only for short-lived technical functionality. | GDPR Art. 5(1)(c) Data minimization; GDPR Art. 5(1)(b) Purpose limitation | Inspect Session Storage entries during an active browsing session and assess their function. Example: In DevTools → Application → Session Storage, observe temporary values such as page state or short-lived interaction flags. Refreshing the page or opening a new tab should clear these entries, and no unique identifiers or values that persist across sessions should be present. | TWIPLA uses browser Session Storage solely for transient, session-level technical functionality and does not use it as a cookie or cookie substitute. |
| 4. | Session Storage does not allow identification across browsing sessions. | GDPR Art. 5(1)(c) Data minimization; GDPR Art. 5(1)(e) Storage limitation | Reload the site or start a new session and compare Session Storage values. Positive result: No values persist across sessions, and no identifiers remain stable between page reloads or new sessions. Negative result: One or more values persist unchanged across sessions or enable recognition of the same visitor over time. | TWIPLA does not use Session Storage in a way that enables visitor identification across browsing sessions. |
| 5. | Local Storage does not contain persistent or unique identifiers. | ePrivacy Directive Art. 5(3); GDPR Art. 5(1)(c) Data minimization | Inspect Local Storage values and monitor whether identifiers persist across visits. Positive result: Local Storage is empty or contains only non-identifying configuration values that do not enable visitor recognition across visits. Negative result: Persistent or unique values remain stored across visits and could be used to recognize or re-identify a returning visitor. | TWIPLA does not store persistent or uniquely identifying value in Local Storage. |
| 6. | Disabling cookies does not re-enable tracking via browser storage. | ePrivacy Directive Art. 5(3); GDPR Art. 5(1)(a) Lawfulness and fairness; GDPR Art. 6(1) | Disable cookies in the browser and observe whether identification or tracking persists. Positive result: No identifiers or tracking mechanisms persist once cookies are disabled, and no alternative browser storage (for example, Local Storage or Session Storage) is used to recreate cookie-like tracking or visitor recognition. Negative result: Tracking, visitor recognition, or identifiers continue to persist despite cookies being disabled, indicating the use of browser storage or other mechanisms to bypass cookie restrictions. | TWIPLA does not use browser storage to recreate cookie-like tracking or visitor identification when cookies are disabled. |
| 7. | All client-side storage behavior is clearly documented and explainable. | GDPR Art. 12; GDPR Art. 13 | Compare observed storage behavior with information provided in privacy documentation. Positive result: All observed storage behavior matches the documented descriptions, purposes, and limitations, and no undocumented or unexplained storage entries or identifiers are present. Negative result: Client-side storage behavior is inconsistent with documentation, insufficiently explained, or includes undocumented values, identifiers, or purposes that cannot be clearly justified or verified. | TWIPLA documents its client-side storage usage in its privacy and product documentation, and the described behavior can be independently verified through browser inspection. |
Assess Fingerprinting and Visitor Identification
Fingerprinting and visitor identification mechanisms determine whether a service can recognize or re-identify visitors without relying on traditional storage mechanisms. Attention is given to whether a non-essential service uses fingerprinting, probabilistic methods, or other indirect identification techniques when embedded on a website, and whether such behavior can be observed and assessed against GDPR and ePrivacy requirements.
Verification Guidance
When reviewing fingerprinting and identification behavior:
- Use multiple browsers and devices where possible
- Test with cookies and browser storage disabled where feasible
- Reload pages multiple times to check for values that remain stable
- Compare network request payloads, not only browser storage
- Start new sessions and compare whether the same values or patterns reappear
- Watch for high-entropy values, or repeated combinations of signals transmitted together
- Cross-check observed behavior against the service’s privacy and technical documentation
- If a tool claims “cookieless,” verify whether recognition still occurs through request data or signal combinations
- Optionally compare findings against known fingerprinting patterns using a public reference, for example, the https://fingerprints.github.io/fingerprints/Fingerprints demo site
Compliance Checklist
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 1. | Non-essential services must not use fingerprinting without valid consent. | ePrivacy Directive Art. 5(3); GDPR Art. 6(1)(a) | Inspect network requests, browser storage, and request payloads for patterns consistent with fingerprinting techniques, such as stable high-entropy identifiers, cross-session persistence, or identifiers derived from combined device or browser attributes. Verification should be based on observed behavior across sessions and configurations, not a single script snapshot. Positive result: No stable or high-entropy identifiers are observed, no identifiers persist across sessions, and no combined technical signals are used to derive a consistent visitor identity prior to valid consent. Negative result: Stable identifiers, cross-session persistence, or identifiers derived from combined technical signals are observed without valid consent, indicating fingerprinting behavior. | TWIPLA operates without any applied identification technology where Maximum Privacy Mode is enabled. |
How this requirement is verified in practice:
- Browser path: right-click → Inspect → Network; Application → Storage.
- Load the website for the first time, keep the consent banner visible, and open the browser’s developer tools before interacting with the banner.
- In Network, review requests made on initial page load and check whether any requests transmit stable identifiers before consent.
- In Application → Storage, confirm that no persistent identifiers are stored at this stage.
- The screenshot shows scripts loading while the banner is still displayed.
- To verify compliance for this requirement, confirm that no visitor identifier is generated or stored before consent, based on the combined checks described in the checklist below.
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 2. | Visitor identification must not rely on probabilistic or derived identifiers. | GDPR Art. 5(1)(a) Lawfulness and fairness; GDPR Art. 5(1)(c) Data minimization; GDPR Art. 6(1) | Review request payloads, transmitted parameters, and stored values for evidence that multiple technical signals (e.g., device characteristics, browser attributes, timing patterns) are combined or correlated to recognize returning visitors. Positive result: No combined or correlated technical signals are used to probabilistically recognize or re-identify visitors. Negative result: Multiple technical signals are combined or correlated in a way that enables probabilistic or derived visitor identification. | Where Maximum Privacy Mode is applied, TWIPLA does not combine technical signals to create probabilistic or derived visitor identifiers. |
| 3. | Services must not silently recreate identifiers across browsing sessions. | ePrivacy Directive Art. 5(3); GDPR Art. 5(1)(a) Lawfulness and fairness; GDPR Art. 5(1)(e) Storage limitation | Clear browser storage, reload the site, or start a new browsing session, and compare transmitted values or request patterns across sessions to determine whether identifiers are recreated or remain stable. Positive result: No identifiers are recreated, reused, or remain stable across sessions once storage is cleared. Negative result: Identifiers are recreated or remain consistent across sessions despite storage being cleared, enabling visitor recognition. | Where Maximum Privacy Mode is applied, TWIPLA does not recreate visitor identifiers across browsing sessions. |
| 4. | Identification methods must be transparent and explainable. | GDPR Art. 12; GDPR Art. 13 | Compare observed identification behavior, request data, and storage usage with the descriptions provided in privacy notices and technical documentation. Positive result: All observed identification behavior aligns with documented descriptions, purposes, and limitations, and no undocumented identifiers or mechanisms are present. Negative result: Identification behavior is inconsistent with documentation, insufficiently explained, or includes undocumented identifiers or mechanisms. | TWIPLA documents its identification methods by privacy mode, and the applied behavior can be independently verified through browser inspection. |
| 5. | Visitor identification must respect consent choices. | GDPR Art. 7; GDPR Art. 6(1)(a); GDPR Art. 5(1)(a) Lawfulness and fairness | Observe identification behavior before consent is given, after consent is granted, and after consent is withdrawn, and compare whether behavior changes consistently with consent status. Positive result: Identification behavior changes appropriately based on consent status and is applied consistently before consent, after consent is granted, and after consent withdrawal. Negative result: Identification behavior does not change based on consent status, or continues unchanged after consent is refused or withdrawn. | TWIPLA allows visitor identification behavior to be configured based on consent status and regional requirements, and applies the selected behavior consistently before consent, after consent, and after consent withdrawal. |
| 6. | Services must not continue visitor identification by switching to alternative identification methods after consent is refused or withdrawn. | ePrivacy Directive Art. 5(3); GDPR Art. 5(1)(a) Lawfulness and fairness; GDPR Art. 6(1) | Refuse or withdraw consent, disable cookies and browser storage, and observe whether visitor identification persists through alternative techniques such as fingerprinting or derived identifiers. Positive result: No visitor identification persists after consent refusal or withdrawal, and no alternative identification techniques are observed. Negative result: Visitor identification continues after consent refusal or withdrawal through alternative or substitute identification methods. | When consent is refused or withdrawn, TWIPLA can be configured to switch to Maximum Privacy Mode, in which no fingerprinting or alternative identification techniques are applied. |
Verify Consent Handling and Legal Basis
Consent handling and lawful basis determine whether data processing is permitted and under which conditions it may occur. The focus here is on how a non-essential service applies consent states and lawful bases in actual system behavior when embedded on a website, and whether observed processing aligns with GDPR and ePrivacy requirements across different consent scenarios.
Verification Guidance
When validating consent handling:
- Always test before consent, after consent is given, and after consent is withdrawn
- Clear browser storage and reload between checks
- Inspect both browser storage and network requests during each consent state
- Reload pages and navigate between pages to confirm the consent state is consistently enforced
- Verify that integration behavior changes immediately when consent status changes
- Verify that consent handling behavior aligns with region-specific configuration, where applicable
- Do not rely solely on the consent banner appearance to assess consent handling
Compliance Checklist
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 1. | No consent-dependent tracking or processing should occur before consent where consent is required. | ePrivacy Directive Art. 5(3); GDPR Art. 6(1)(a) | Load the site without interacting with the consent interface and monitor network requests and browser storage activity. Positive result: No consent-dependent tracking, processing, or storage activity occurs before consent is given. Negative result: Tracking, processing, or storage activity that depends on consent occurs before consent is given. | Where consent is required, TWIPLA does not perform analytics tracking before consent is given. Where consent is not required, TWIPLA can operate in Maximum Privacy Mode without applying consent-dependent tracking. |
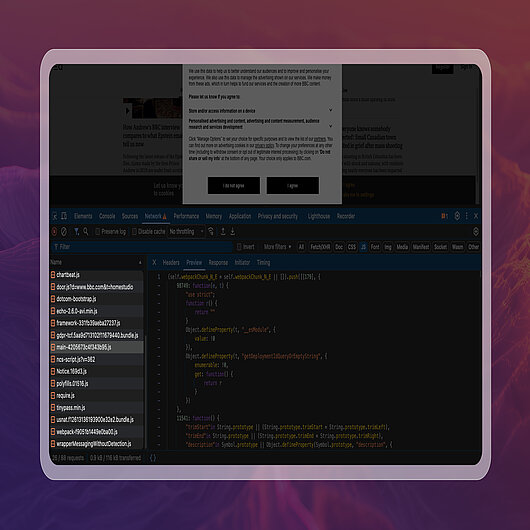
How this requirement is verified in practice:
- Browser path: right-click → Inspect → Network
- Load the website for the first time, keep the consent banner visible, and open the browser’s developer tools before interacting with the banner.
- In the Network panel, review requests triggered on initial page load to check whether any tracking occurs at this stage.
- The screenshot shows network requests loading while the banner is still displayed.
- To verify compliance with this requirement, confirm that no tracking requests occur before consent is given.
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 2. | Personal data must be processed under a valid lawful basis. | GDPR Art. 6(1); ePrivacy Directive Art. 5(3) where storage or access to terminal equipment is involved | Review declared lawful basis in documentation and verify that observed data collection and processing behavior matches the stated lawful basis. Positive result: Observed processing behavior aligns with the declared lawful basis and applicable legal requirements. Negative result: Processing behavior does not align with the declared lawful basis or lacks a valid lawful basis. | TWIPLA allows processing to be configured in line with the applicable lawful basis and applies data collection behavior that corresponds to the selected basis and regional requirements. |
| 3. | Data collection must respect user consent choices where consent is relied upon. | GDPR Art. 6(1)(a); GDPR Art. 5(1)(a) Lawfulness and fairness | Compare network requests and browser storage usage before consent, after consent is granted, and when consent is not given. Positive result: Data collection behavior changes appropriately based on the user’s consent choice. Negative result: Data collection behavior does not change or continues unchanged despite the user’s consent choice. | TWIPLA allows data collection behavior to change based on consent status, applying different behavior before consent, after consent is granted, and when consent is not given. |
| 4. | Where consent is required, consent must be informed, specific, and freely given before any consent-based processing begins. | GDPR Art. 4(11); GDPR Art. 7; GDPR Art. 12; GDPR Art. 13; ePrivacy Directive Art. 5(3) | Review the consent prompt for clear purposes, granular choices where relevant, equal ease of refusal, and access to detailed information, then confirm no consent-based requests occur until consent is obtained. Positive result: Consent is presented clearly and freely, and no consent-based processing occurs before consent is given. Negative result: Consent is unclear, coerced, bundled, or consent-based processing occurs before consent is obtained. | Where consent is required, TWIPLA can be configured so consent-based tracking does not start until consent is obtained, and the applied behavior can be verified through network and storage inspection. |
| 5. | Consent refusal must prevent consent-based tracking or processing. | GDPR Art. 6(1)(a); GDPR Art. 5(1)(a) Lawfulness and fairness | Explicitly refuse consent and observe whether consent-dependent tracking, processing, or storage occurs. Positive result: No consent-based tracking or processing occurs after consent is refused. Negative result: Consent-based tracking or processing occurs despite consent being refused. | When consent is refused, TWIPLA disables tracking that relies on visitor consent. |
| 6. | Consent withdrawal must be honoured. | GDPR Art. 7(3); GDPR Art. 5(1)(a) Lawfulness and fairness | Withdraw consent and verify that consent-based tracking or processing stops and does not resume unless consent is given again. Positive result: Consent-based processing stops after withdrawal and does not resume without renewed consent. Negative result: Consent-based processing continues or resumes without renewed consent. | When consent is withdrawn, TWIPLA does not activate consent-based tracking and does not resume such tracking unless consent is given again. |
| 7. | Consent must not be bypassed via alternative tracking or identification mechanisms. | ePrivacy Directive Art. 5(3); GDPR Art. 5(1)(a) Lawfulness and fairness; GDPR Art. 6(1) | Disable cookies and relevant browser storage, refuse or withdraw consent, and observe whether tracking or identification persists through other mechanisms. Positive result: No tracking or identification persists after consent refusal or withdrawal. Negative result: Tracking or identification persists through alternative or substitute mechanisms despite consent refusal or withdrawal. | TWIPLA does not bypass consent by switching to alternative tracking mechanisms. When consent is refused or withdrawn, it can be configured to switch to Maximum Privacy Mode, in which no consent-dependent identification or substitute tracking methods are applied. |
| 8. | Legitimate interest claims must be limited, necessary, and defensible. | GDPR Art. 6(1)(f); GDPR Art. 5(1)(c) Data minimization; Recital 47 | Review legitimate interest documentation and assess whether the scope of collected data aligns with necessity, proportionality, and the stated purpose. Positive result: Data collection is limited to what is necessary and proportionate to the stated legitimate interest. Negative result: Data collection exceeds what is necessary or cannot be reasonably justified under legitimate interest. | When legitimate interest is relied upon, TWIPLA can be configured to limit data collection to proportionate, non-intrusive behavior that supports a defensible legitimate interest assessment. |
| 9. | Consent and lawful-basis behavior must be applied consistently for EU data subjects. | GDPR Art. 5(1)(a) Lawfulness and fairness | Test site behavior from EU and non-EU locations and verify that EU users receive compliant consent handling and lawful-basis processing behavior. Positive result: EU users are consistently subject to compliant consent handling and lawful-basis behavior. Negative result: EU users receive non-compliant or inconsistent consent or lawful-basis handling. | TWIPLA allows consent and lawful-basis behavior to be applied consistently for EU data subjects through region-aware privacy configuration, with GDPR Privacy Mode meeting GDPR requirements and Maximum Privacy Mode meeting the higher combined GDPR and ePrivacy threshold. |
Inspect Data Transmission and Hosting Location
Data transmission paths and hosting locations determine where data is processed, stored, and accessed, and whether cross-border transfers occur. Attention is placed on how a non-essential service transmits data and where processing takes place when embedded on a website, including whether observed behavior aligns with GDPR requirements for international transfers and post-Schrems II safeguards.
Verification Guidance
When validating data transmission and hosting:
- Inspect all network request destinations, not only primary endpoints
- Resolve integration-related domains to IP addresses and verify hosting location using independent lookup tools (for example, https://check-host.net/ip-info)
- Pay attention to redirects, fallbacks, and secondary request destinations
- Distinguish content delivery or asset endpoints from data processing or storage endpoints
- Test both initial page loads and subsequent interactions to observe transmission behavior
- Where possible, test from different locations or configurations to identify routing differences
- Cross-check observed hosting and data transfer behavior against documentation and contractual disclosures
Compliance Checklist
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 1. | Sub-processors involved in hosting or data transmission must be disclosed and contractually governed. | GDPR Art. 28(2), Art. 28(4) | Review sub-processor disclosures, data processing agreements (DPAs), and contractual safeguards. Positive result: Sub-processors are clearly disclosed, roles are defined, and contractual safeguards (including required terms under Art. 28) are documented. Negative result: Sub-processors are not disclosed, contracts are missing or unclear, or required safeguards for sub-processing are not evidenced. | TWIPLA discloses its sub-processors and governs their involvement through contractual data processing agreements that define scope and data protection obligations. |
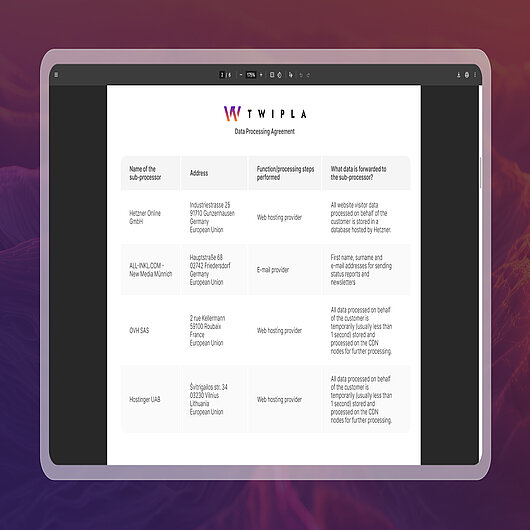
How this requirement is verified in practice:
- Source: Data Processing Agreement → Sub-processor list
- Review the integration’s DPA and locate the section listing disclosed processors.
- Confirm that hosting and infrastructure providers involved in data transmission are explicitly named, along with their addresses and functions.
- The screenshot shows an excerpt from TWIPLA’s published sub-processor list.
- To verify compliance with this requirement, confirm that all relevant sub-processors are disclosed and governed by contractual data processing agreements, as reflected in the checklist below.
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 2. | Data processing must comply with GDPR international transfer requirements where data leaves the EU or EEA. | GDPR Chapter V (Art. 44–49) | Inspect network request destinations (domains, IPs, and endpoints), documented processing locations, and data flow descriptions. Positive result: Where data leaves the EU or EEA, transfers are identified, and a lawful transfer mechanism under Chapter V is documented and applicable. Negative result: Data appears to leave the EU or EEA without an identified transfer mechanism, or transfer documentation is missing or inconsistent with observed behavior. | TWIPLA processes analytics data exclusively in EU-based data centers located in Germany, so no international data transfers outside the EU occur. |
| 3. | Transfers of personal data to third countries must be subject to appropriate safeguards. | GDPR Art. 44–46; Schrems II (C-311/18) | Review applicable transfer mechanisms (for example, adequacy decisions or Standard Contractual Clauses) and documented supplementary measures where relevant. Positive result: A valid transfer mechanism is in place for any third-country transfer, and supplementary measures are documented where needed. Negative result: Transfers occur without a valid mechanism, or safeguards are not evidenced or do not align with the transfer context. | TWIPLA processes analytics data within the EU, so transfers of personal data to third countries do not occur. |
| 4. | Service delivery must minimize unnecessary third-country exposure through technical design choices. | GDPR Art. 25 Data protection by design; GDPR Art. 5(1)(a) Lawfulness and fairness | Inspect request domains, routing, and third-party endpoints in browser developer tools to assess use of first-party or controlled endpoints and identify reliance on third-country infrastructure where avoidable. Positive result: Delivery is routed through controlled or appropriate endpoints and avoids unnecessary third-country exposure by design. Negative result: Delivery relies on third-country endpoints or infrastructure unnecessarily, increasing exposure without clear justification or controls. | TWIPLA delivers analytics via controlled, EU-hosted processing endpoints and a content delivery network for asset delivery. Analytics processing remains within the EU, and optional first-party or region-specific delivery can be used to minimize unnecessary third-country exposure by design. |
| 5. | Hosting and infrastructure arrangements must not undermine the effectiveness of GDPR protections. | GDPR Art. 44; Schrems II (C-311/18) | Identify hosting provider jurisdiction and assess documented transfer risk assessments and mitigation measures where applicable. Positive result: Hosting arrangements support effective GDPR protections, and documented risk assessments and mitigations address identified risks where relevant. Negative result: Hosting arrangements introduce unresolved risks, such as access risks, that are not assessed or mitigated, undermining effective protection. | TWIPLA relies on infrastructure providers operating under EU jurisdiction, so hosting and processing arrangements remain subject to EU law and do not undermine the effectiveness of GDPR protections. |
| 6. | Hosting provider jurisdiction should be assessed for third-country access risk, including exposure under the US CLOUD Act where applicable. | GDPR Art. 44–46; Schrems II (C-311/18) | Identify the hosting provider jurisdiction and corporate control, then assess whether data could be subject to third-country access requests even if data is stored in the EU. Positive result: Jurisdictional and access risks are identified and assessed, and mitigations are documented where relevant. Negative result: Jurisdictional or access risks are not assessed, or the setup creates unmitigated exposure to third-country access. | TWIPLA processes analytics data in EU-based data centers in Germany under EU jurisdiction, minimizing third-country access exposure and avoiding routine transfers outside the EU. |
| 7. | Personal data must be protected during transmission using appropriate technical security measures. | GDPR Art. 32(1)(a) Security of processing | Inspect request protocols (HTTPS/TLS), certificates, and transport-level security indicators. Positive result: Data is transmitted over HTTPS with valid TLS, and no insecure downgrade or mixed-content transmission is observed. Negative result: Data is transmitted over HTTP, weak or invalid TLS is observed, or mixed-content or insecure transmission occurs. | TWIPLA transmits analytics data over HTTPS using TLS encryption to protect data in transit. |
| 8. | Actual data transmission and hosting behavior must align with published privacy documentation. | GDPR Art. 12; GDPR Art. 13; GDPR Art. 5(1)(a) Transparency | Compare observed network destinations, data flows, and hosting indicators with published privacy notices and technical documentation. Positive result: Observed transmission and hosting behavior matches documented descriptions, including locations and relevant parties. Negative result: Observed behavior conflicts with documentation, or material details such as destinations, providers, or locations are missing or unclear. | TWIPLA’s published privacy documentation and technical descriptions accurately reflect the data transmission and hosting behavior observable in network inspection. |
Reference Documentation
→ Inspecting network request destinations in browser DevTools (Chrome DevTools docs)
→ Resolving domains to IP addresses and hosting location (check-host.net)
→ Identifying redirects and secondary request destinations (Chrome DevTools docs)
→ Verifying HTTPS and TLS security in browser requests (Chrome DevTools docs)
Evaluate Data Minimization and Purpose Limitation
Data minimization and purpose limitation define whether personal data collection is confined to what is necessary for a clearly stated objective. The assessment considers whether a non-essential service limits collection to relevant data only, applies proportional defaults, and avoids expanded or optional data collection beyond the stated purpose, in line with GDPR principles.
Verification Guidance
When assessing data minimization:
- inspect actual network request payloads, not only browser storage
- Identify each data field transmitted and assess whether it is required for the stated purpose of the integration
- Pay attention to optional parameters, metadata, and contextual attributes included in requests
- Test the default configuration before enabling any optional or advanced features
- Compare data collected before and after enabling optional features or components
- Compare data collection behavior across different components or functions of the integration to identify differences in scope
- Verify that sensitive, excessive, or irrelevant attributes are not collected by default
Compliance Checklist
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 1. | Services must collect only data that is necessary for their stated purposes. | GDPR Art. 5(1)(c) Data minimization | Review request payloads and stored values to identify data fields that are not necessary for the declared purpose. Positive result: Only data fields that are necessary for the stated purpose are collected and transmitted. Negative result: Superfluous or unrelated data fields are collected or transmitted without clear necessity for the stated purpose. | TWIPLA limits data collection to information strictly necessary for aggregated analytics and behavioral insights, and does not collect superfluous data unrelated to its stated analytics purposes. |
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 2. | Personal data must be collected for explicit, specified, and legitimate purposes only. | GDPR Art. 5(1)(b) Purpose limitation | Compare observed data collection and processing behavior with documented purposes in privacy documentation. Positive result: Observed collection and processing align with explicit documented purposes. Negative result: Data is collected or processed in ways that do not align with documented purposes, or purposes are vague or not specific enough to assess. | TWIPLA defines clear and explicit analytics purposes and restricts data collection and processing to what is necessary to fulfil those documented purposes. |
| 3. | Default configuration must limit data collection to what is necessary. | GDPR Art. 25(2) Privacy by default; GDPR Art. 5(1)(c) Data minimization | Install or enable the service with default settings and observe initial data collection behavior. Positive result: Default behavior is limited to what is necessary for the stated purpose, without optional or expanded collection enabled by default. Negative result: Default behavior includes optional, expanded, or excessive collection beyond what is necessary for the stated purpose. | During onboarding, TWIPLA pre-selects Maximum Privacy Mode, ensuring privacy-by-default data minimization unless the user explicitly chooses a different configuration. |
| 4. | Service design should support configurable data collection to align with different privacy requirements. | GDPR Art. 25(1) Privacy by design | Review available configuration options and privacy controls that affect data collection scope and depth. Positive result: The service provides meaningful controls to reduce or adjust the collection scope in line with different regulatory or organizational requirements. Negative result: The service lacks practical controls to limit collection, or configuration options do not materially affect collection scope. | TWIPLA provides configurable privacy modes that allow organisations to align data collection depth with different regulatory requirements, including GDPR and ePrivacy thresholds. |
| 5. | Optional or non-essential data points must not be collected without a valid lawful basis. | GDPR Art. 6(1); GDPR Art. 5(1)(a) Lawfulness and fairness | Inspect request payloads and storage for optional attributes and assess whether a valid lawful basis is defined and applied for their collection. Positive result: Optional or non-essential attributes are not collected unless enabled and supported by a valid lawful basis. Negative result: Optional or non-essential attributes are collected without a defined lawful basis, or are collected by default without a clear justification. | TWIPLA does not collect non-essential or optional data attributes unless they are explicitly enabled through configuration and supported by a valid lawful basis. |
| 6. | Where aggregated data is sufficient to achieve the stated purpose, the collection of individual-level personal data should be avoided. | GDPR Art. 5(1)(c) Data minimization | Review whether individual-level identifiers are necessary for the stated purpose or whether aggregated data would meet the stated purpose. Positive result: Aggregated data is used where it can fulfil the purpose, and individual-level data is limited to what is necessary. Negative result: Individual-level personal data or identifiers are collected where aggregated reporting would reasonably meet the stated purpose. | TWIPLA uses aggregated analytics wherever individual-level personal data is not necessary. |
| 7. | Data minimization principles must be applied consistently across features and modules. | GDPR Art. 5(1)(c) Data minimization | Compare data collection behavior across different modules and features to confirm consistent limits on scope and collection depth. Positive result: Data minimization controls and collection limits are applied consistently across modules and features. Negative result: Some modules collect materially more data than others without a clear necessity for their stated purpose or without appropriate controls. | TWIPLA applies the same data minimization standards across all analytics modules, ensuring consistent limits on data scope and collection depth. |
Reference Documentation
→ Inspecting network request payloads in browser DevTools (Chrome DevTools docs)
→ Analyzing request parameters and payload data (Chrome DevTools docs)
→ Comparing network requests before and after configuration changes (Chrome DevTools docs)
→ Identifying unnecessary or excessive request data (Chrome DevTools docs)
→ TWIPLA GDPR purpose limitation principles overview
→ TWIPLA Data Processing Agreement, scope and data minimization
→ TWIPLA Maximum Privacy Mode, default privacy behavior
Confirm Data Retention and Deletion Practices
Data retention and deletion practices determine how long personal data remains available and whether it is removed once it is no longer necessary for its stated purpose. The assessment examines whether a non-essential service defines retention limits, applies deletion consistently across its components, and ensures that data is no longer accessible once retention periods expire, in line with GDPR requirements.
Verification Guidance
When validating retention and deletion behavior:
- Review documented default and custom data retention settings
- Check whether historical data remains accessible after defined retention periods expire
- Verify that data is deleted, anonymized, or otherwise made inaccessible once retention limits are reached
- Confirm that deletion applies across all components, modules, or derived datasets of the integration
- Verify that deletion behavior is applied consistently across configurations and access paths
- Check whether deletion propagates to backups and replicas within documented timeframes
- Cross-check observed retention and deletion behavior against documented retention periods and deletion obligations
Compliance Checklist
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 1. | Retention periods must be transparent and clearly documented. | GDPR Art. 13; GDPR Art. 12 | Review privacy notices, retention disclosures, and supporting documentation describing retention periods. Positive result: Retention periods or retention criteria are clearly documented and accessible. Negative result: Retention periods are missing, unclear, or not documented in a way that allows verification. | TWIPLA transparently documents its data retention behavior and allows organisations to determine how long analytics data remains available based on their chosen configuration and analytics needs. |
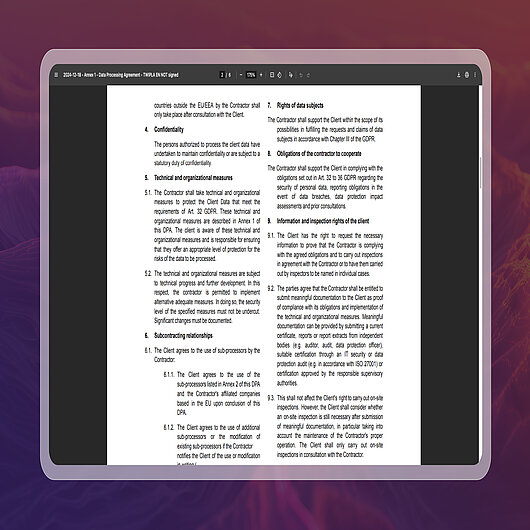
How this requirement is verified in practice:
- Source: Data Processing Agreement → Retention and deletion provisions
- Review the provider’s Data Processing Agreement and locate the sections defining data retention periods and deletion or return obligations.
- Confirm that retention limits, deletion requirements, and related responsibilities are explicitly documented.
- The screenshot shows an excerpt from TWIPLA’s Data Processing Agreement outlining retention and deletion obligations.
- To verify compliance for this requirement, confirm that data retention and deletion practices are contractually defined and transparently disclosed, as reflected in the checklist below.
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 2. | Personal data must not be retained longer than necessary for the stated purpose. | GDPR Art. 5(1)(e) Storage limitation | Review retention settings, retention policies, and the availability of historical data over time. Positive result: Data is retained only for as long as necessary to fulfil the stated purpose. Negative result: Data is retained indefinitely or longer than necessary without documented justification. | TWIPLA applies purpose-based data retention controls, allowing analytics data to be retained only for as long as it remains necessary for the controller’s stated analytics purposes, including long-term trend analysis where required. |
| 3. | Retention mechanisms must ensure that data is no longer available once the retention period expires. | GDPR Art. 5(1)(e) Storage limitation | Observe whether data older than the defined retention period is deleted, anonymized, or otherwise no longer accessible. Positive result: Data beyond the defined retention period is no longer available or accessible. Negative result: Data remains accessible beyond the documented retention period. | TWIPLA ensures analytics data is no longer retained when processing ends or upon the client’s instruction, in line with documented retention obligations and GDPR storage limitation requirements. |
| 4. | Personal data must be erasable where required under data subject rights. | GDPR Art. 17 Right to erasure; GDPR Art. 12 | Verify whether data can be deleted or excluded in response to erasure requests through documented processes. Positive result: Erasure or exclusion mechanisms exist and can be executed in response to valid data subject requests. Negative result: Erasure requests cannot be fulfilled, or deletion mechanisms are undocumented or ineffective. | TWIPLA supports the right to erasure by enabling deletion or exclusion of personal data in response to data subject requests, based on documented processes and controller instructions. |
| 5. | Ongoing access to retained data must respect current privacy and access settings. | GDPR Art. 5(1)(a) Lawfulness and fairness; GDPR Art. 25 Privacy by design | Change privacy or access settings and assess whether access to retained historical data is appropriately restricted. Positive result: Access to retained data reflects current privacy and access settings. Negative result: Retained data remains accessible in ways that conflict with updated privacy or access controls. | TWIPLA ensures access to retained analytics data respects current privacy configuration and controller-defined access controls. |
| 6. | Actual retention and deletion behavior must align with documented retention policies. | GDPR Art. 5(2) Accountability | Compare observed data availability and deletion behavior with published retention policies and internal documentation. Positive result: Observed retention and deletion behavior matches documented policies. Negative result: Observed behavior conflicts with documented retention or deletion commitments. | TWIPLA’s actual data retention and deletion behavior is consistent with its documented data handling and retention policies, supporting GDPR accountability requirements. |
| 7. | Retained data must remain limited and proportionate to the stated purpose. | GDPR Art. 5(1)(c) Data minimization | Review the scope, granularity, and age of retained datasets to assess whether they remain necessary for the stated purpose. Positive result: Retained data remains proportionate in scope and granularity to the stated purpose. Negative result: Retained datasets exceed what is necessary in scope, detail, or duration. | TWIPLA ensures that retained data remains limited in scope and granularity to what is necessary for analytics and reporting purposes. |
| 8. | Retention and deletion obligations must apply to all subprocessors processing personal data. | GDPR Art. 28(4); GDPR Art. 5(1)(e) Storage limitation | Review the approved subprocessors list and data processing agreements to confirm that subprocessors are contractually required to apply deletion and retention obligations in line with documented periods and controller instructions. Positive result: Subprocessors are contractually bound to retention and deletion obligations aligned with the controller’s instructions. Negative result: Subprocessors are not subject to equivalent retention and deletion obligations. | TWIPLA uses approved, documented subprocessors under agreements that correspond to its Data Processing Agreement and require deletion of analytics data in line with documented retention periods and controller instructions. |
Validate Data Subject Rights and Access Controls
Data subject rights and access controls determine whether personal data can be accessed, managed, and acted upon in line with GDPR obligations. The assessment considers how a non-essential service restricts access to data, supports the exercise of data subject rights in practice, and applies role-based controls and accountability measures within an organization.
Verification Guidance
When reviewing support for data subject rights:
- Clarify whether data processed by the integration constitutes personal data in the given configuration
- Test access and deletion processes using non-production or test data where possible
- Verify that access and erasure requests can be fulfilled within statutory response deadlines
- Confirm that appropriate identity verification is required before fulfilling data subject requests
- Verify that responses to data subject requests include all relevant personal data processed by the integration
- Confirm who within the organization can access processed personal data and under which roles or permissions
- Review whether access controls follow the principle of least privilege
- Check that access and data subject request actions are logged, traceable, or auditable
Compliance Checklist
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 1. | Access to personal data must be restricted to authorised personnel. | GDPR Art. 32(1)(b); GDPR Art. 5(1)(f) Integrity and confidentiality | Review user roles, permissions, and access levels to confirm appropriate access restrictions. Positive result: Access to personal data is limited to authorised roles and permissions, with least-privilege controls evident. Negative result: Personal data is accessible to unauthorised roles, or permissions are overly broad. | TWIPLA enforces role-based access controls to ensure analytics data is accessible only to authorised personnel. |
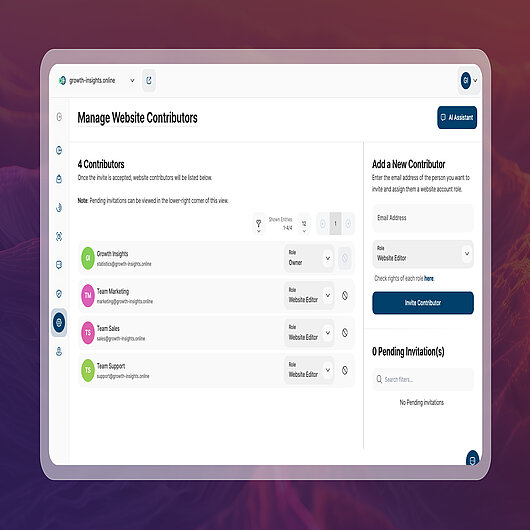
How to verify this example requirement:
- Source: Integration access management or contributor overview.
- Review the access management or contributor settings of a website integration to identify which users can access processed data and what roles or permission levels are assigned.
- Confirm that access is restricted to authorized personnel and that roles are clearly defined.
- The screenshot shows an example of a contributor management view from the TWIPLA platform.
- To verify compliance for this requirement, confirm that access to processed data is controlled through role-based permissions and supports accountability, as reflected in the checklist below.
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 2. | Data subjects must be able to exercise their right of access where personal data is processed. | GDPR Art. 15 | Assess whether personal data processed by the service can be identified, retrieved, and provided in an intelligible form upon request. Positive result: Relevant personal data can be retrieved and provided in an intelligible form, subject to applicable conditions and scope. Negative result: Personal data cannot be reliably retrieved, is incomplete, or cannot be provided in an intelligible form. | TWIPLA enables controllers to retrieve and present personal analytics data in a structured, intelligible form to support data subject access requests. |
| 3. | Data subjects must be able to request erasure of personal data where the right applies. | GDPR Art. 17; GDPR Art. 12 | Verify whether personal data can be deleted or excluded in response to an erasure request, subject to applicable exemptions. Positive result: Erasure or exclusion can be executed through documented processes, and outcomes can be confirmed, subject to applicable exemptions. Negative result: Erasure requests cannot be fulfilled in practice, or processes are undocumented or ineffective. | TWIPLA enables deletion or exclusion of personal analytics data in response to erasure requests, based on documented controller instructions and applicable GDPR requirements. |
| 4. | Objection to processing must be supported where processing is based on legitimate interest or public task. | GDPR Art. 21 | Review processing purposes and configuration options to determine whether processing can be limited or ceased following an objection. Positive result: Processing can be limited or ceased for the relevant purpose following a valid objection, where required. Negative result: Processing cannot be limited or ceased following an objection where the right applies. | TWIPLA supports objections to processing by enabling controllers to limit or cease analytics data processing through privacy modes and configuration controls, where processing is based on legitimate interest or public task. |
| 5. | Data portability must be supported where the right applies. | GDPR Art. 20 | Check whether personal data provided by the data subject can be exported in a structured, commonly used, machine-readable format where processing is based on consent or contract. Positive result: Export is available in an appropriate format for the relevant personal data, where Art. 20 applies. Negative result: Export is not possible or not provided in an appropriate format where Art. 20 applies. | TWIPLA provides data export capabilities for analytics data to the extent data portability under GDPR Art. 20 applies, taking into account the nature and scope of personal data processed. |
| 6. | Only authorised users should be able to access personal data. | GDPR Art. 5(1)(f) Integrity and confidentiality | Attempt access using accounts with different permission levels to verify enforcement of access controls. Positive result: Unauthorised accounts cannot access personal data, and access is consistently enforced by role or permission level. Negative result: Unauthorised accounts can access personal data, or restrictions are inconsistently enforced. | TWIPLA enforces role-based access controls so only authorised users can access analytics data. |
| 7. | Access to personal data should be traceable to support accountability. | GDPR Art. 5(2) Accountability | Review available access logs, audit trails, or documented procedures relating to data access. Positive result: Access is traceable through logs, audit trails, or equivalent documented procedures that support accountability. Negative result: Access is not traceable, and there is no reliable audit trail or equivalent procedure. | TWIPLA supports accountability by enforcing controlled access and maintaining documented procedures governing analytics data access. |
| 8. | Controllers must be able to facilitate data subject requests without undue delay. | GDPR Art. 12(2); GDPR Art. 12(3) | Assess the operational steps required to identify, retrieve, and act upon a data subject request within statutory time limits. Positive result: The process enables timely identification, retrieval, and action within statutory deadlines. Negative result: The process is not feasible within statutory deadlines due to missing capability, excessive manual effort, or unclear procedures. | TWIPLA is designed to support the timely identification, retrieval, and handling of data subject requests in line with statutory response deadlines. |
Reference Documentation
→ Understanding data portability and structured exports (ICO guidance)
→ Verifying role-based access controls and least privilege (UK NCSC guidance)
→ Auditing access logs and accountability controls (ISO standard)
→ Handling data subject access and erasure requests operationally (ICO guidance)
Check Data Processing Agreement and Roles
Processing agreements and defined roles establish who is responsible for personal data handling and under what conditions processing may take place. The section examines whether a non-essential service clearly documents controller and processor roles, applies appropriate contractual safeguards, and reflects those obligations consistently in observed data processing behavior under GDPR.
Verification Guidance
When reviewing processing agreements and roles:
- Confirm that controller and processor roles are clearly defined and not contradictory
- Compare documented processing roles and instructions with observed system behavior
- Review whether documented processing instructions are sufficiently specific and limited in scope
- Verify that sub-processors are transparently disclosed and subject to defined notification and objection mechanisms
- Check that contractual commitments align with observed data processing and hosting behavior
- Verify that responsibilities for security, assistance, and compliance obligations are explicitly documented
- Confirm ownership, responsibility, and governance for maintaining the Data Processing Agreement
Compliance Checklist
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 1. | Appropriate technical and organisational measures must be implemented to protect personal data. | GDPR Art. 32 | Review documented security measures, organisational controls, and supporting security documentation. Positive result: Appropriate technical and organisational measures addressing confidentiality, integrity, availability, and resilience are documented and implemented. Negative result: Measures are missing, insufficiently documented, or do not reasonably address the security requirements of Art. 32. | TWIPLA implements and documents appropriate technical and organisational measures, including encryption, access controls, infrastructure security, and availability safeguards, to protect analytics data in line with GDPR Art. 32. |
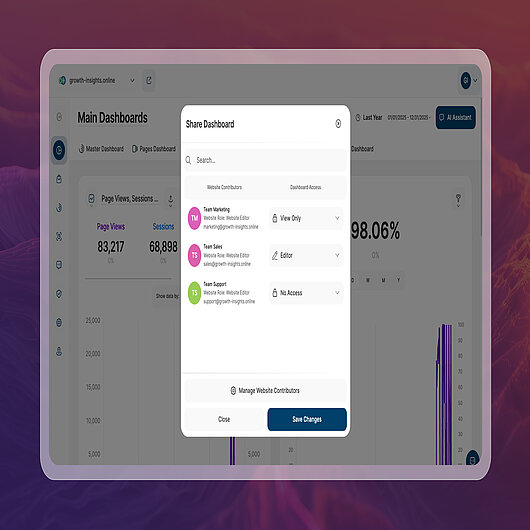
How this requirement is verified in practice:
- Source: Integration access control or permission management view
- Review the integration’s access control or permission management interface to identify which users can access data or functionality and what permission levels are assigned.
- Confirm that access restrictions, such as read-only access, modification rights, or no access, are clearly defined and enforced.
- The screenshot shows an example of a dashboard access control view from the TWIPLA platform.
- To verify compliance for this requirement, confirm that documented roles and contractual access limitations are reflected in actual system behavior, as outlined in the checklist below.
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 2. | The roles of controller and processor must be clearly defined based on actual processing activities. | GDPR Art. 4; GDPR Art. 28 | Review contractual documentation and privacy notices, and compare them with observed processing behavior to confirm role allocation. Positive result: Controller and processor roles are clearly defined and consistent with observed processing activities. Negative result: Roles are unclear, contradictory, or inconsistent with observed processing behavior. | TWIPLA acts as a data processor under GDPR, with its controller–processor role clearly defined in contractual documentation and reflected in actual processing activities. |
| 3. | A Data Processing Agreement must be in place where a processor processes personal data on behalf of a controller. | GDPR Art. 28(3) | Verify the availability, accessibility, and scope of a Data Processing Agreement covering the relevant processing activities. Positive result: A DPA is available, accessible to the controller, and covers the required scope under Art. 28(3). Negative result: No DPA is available, access is restricted, or the agreement does not cover the relevant processing activities. | TWIPLA provides a Data Processing Agreement in accordance with GDPR Art. 28(3), governing its processing of personal data on behalf of the controller. |
| 4. | Processing by the processor must be limited to documented instructions from the controller. | GDPR Art. 28(3)(a) | Review documented instructions in the DPA and assess whether observed processing activities align with those instructions. Positive result: Observed processing aligns with documented instructions and does not exceed the agreed scope. Negative result: Processing exceeds or conflicts with documented instructions, or scope limitations are unclear. | TWIPLA processes analytics data solely on the basis of documented instructions from the controller, as defined in the Data Processing Agreement, unless otherwise required by applicable law. |
| 5. | Use of sub-processors must be transparent and subject to appropriate controls. | GDPR Art. 28(2); GDPR Art. 28(4) | Review sub-processor lists, authorisation mechanisms, and contractual flow-down obligations. Positive result: Sub-processors are transparently disclosed, authorisation or notification mechanisms are in place, and equivalent data protection obligations are contractually imposed. Negative result: Sub-processors are not disclosed, controls are missing, or equivalent contractual safeguards are not in place. | TWIPLA ensures transparent use of sub-processors by maintaining an up-to-date sub-processor list, applying prior notification and objection mechanisms, and contractually binding sub-processors to equivalent data protection obligations. |
| 6. | The processor must assist the controller in fulfilling data subject rights obligations where applicable. | GDPR Art. 28(3)(e) | Review DPA clauses relating to assistance with data subject requests and supporting operational procedures. Positive result: Assistance obligations are documented in the DPA and supported by procedures that enable the controller to fulfil data subject rights. Negative result: Assistance obligations are missing, unclear, or unsupported by documented procedures. | TWIPLA’s DPA requires TWIPLA to assist controllers, upon request, in fulfilling data subject rights under Chapter III of the GDPR through documented procedures. |
| 7. | Contractual commitments must be consistent with actual processing behavior. | GDPR Art. 5(2) Accountability | Compare contractual terms and documented commitments with observable system behavior and processing practices. Positive result: Observable processing behavior is consistent with contractual commitments and documented representations. Negative result: Observable behavior conflicts with contractual commitments or documented representations. | TWIPLA’s contractual processing commitments are demonstrably reflected in actual system behavior and data processing practices. |
Confirm Transparency and Verifiability
Transparency and verifiability determine whether GDPR compliance claims can be independently assessed rather than taken at face value. Observable system behavior, supporting documentation, and consistent technical implementation are examined to assess whether stated compliance accurately reflects how a non-essential service operates in practice.
Verification Guidance
When assessing transparency and verifiability:
- Treat documentation as a reference point, not proof of compliance
- Verify compliance claims using observable system and network behavior
- Change privacy-relevant settings and confirm measurable changes in behavior
- Re-test observed behavior after configuration changes or product updates
- Confirm that verification steps can be reproduced by an independent reviewer using standard tools
- Cross-check findings against other verification steps in this checklist
- Re-assess periodically to confirm behavior remains consistent over time
Compliance Checklist
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 1. | GDPR compliance claims must be demonstrable. | GDPR Art. 5(2) Accountability | Compare documented compliance claims with observable technical and processing behavior. Positive result: Documented claims are supported by observable behavior and evidence (for example, documentation, technical controls, and configuration behavior). Negative result: Claims cannot be substantiated through observable behavior, or conflict with observed behavior or evidence. | TWIPLA’s GDPR compliance claims are demonstrable through observable system behavior, documented processing practices, and verifiable technical controls. |
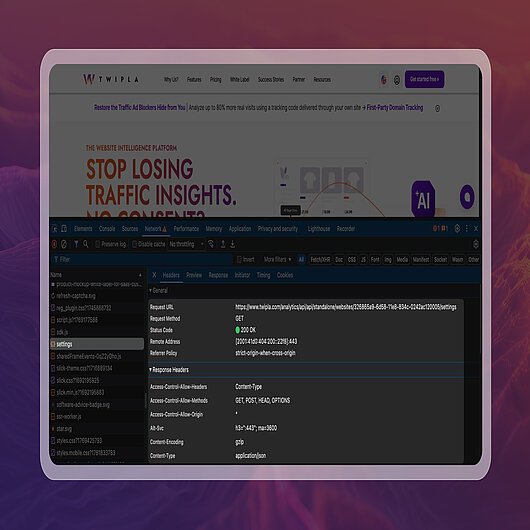
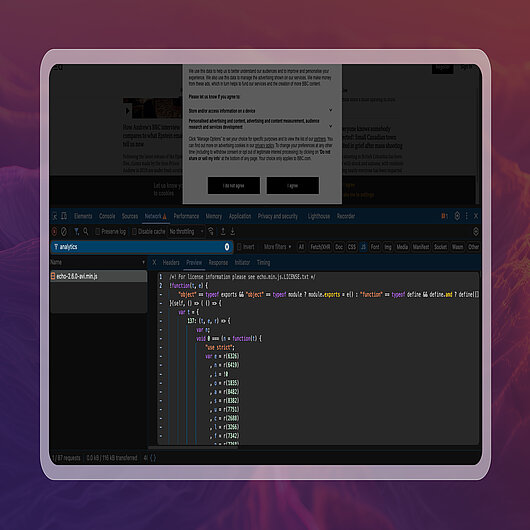
How this requirement is verified in practice:
- Browser path: right-click → Inspect → Network
- Open the browser’s developer tools and load the page normally.
- In the Network panel, review requests sent to endpoints and inspect the associated request headers and parameters.
- The screenshot shows a live analytics settings request sent to a TWIPLA-controlled endpoint.
- To verify compliance for this requirement, confirm that the observed network behavior matches the documented processing behavior and configuration described in the checklist below.
| What to Check | Related Law | Verification Steps & Observable Evidence | How TWIPLA Meets This Requirement | |
| 2. | Personal data flows must be transparent and explainable. | GDPR Art. 12; GDPR Art. 13 | Inspect network requests and review documented data flow explanations to assess transparency. Positive result: Data flow documentation explains what data is transmitted, to whom, and for what purposes, in a way that corresponds with observable network behavior. Negative result: Data flows are unclear, undocumented, or inconsistent with observable network behavior. | TWIPLA provides clear data flow documentation that corresponds directly with observable network behavior, enabling transparent and explainable personal data processing. |
| 3. | Documentation describing processing activities must accurately reflect actual processing. | GDPR Art. 12; GDPR Art. 13; GDPR Art. 5(2) Accountability | Compare privacy and technical documentation with browser-level and network inspection. Positive result: Observed processing behavior matches documented descriptions, including what is processed and how it is transmitted or handled. Negative result: Observed processing behavior conflicts with documentation or includes undocumented processing activity. | TWIPLA’s privacy and technical documentation is aligned with observable browser and network behavior, supporting accurate and verifiable descriptions of processing activities. |
| 4. | Compliance with requirements must be independently verifiable. | GDPR Art. 5(2) Accountability | Attempt verification using standard, non-proprietary tools, such as browser developer tools. Positive result: Key behaviors can be validated using standard tools without relying solely on vendor assertions. Negative result: Verification cannot be performed without proprietary tooling or untestable vendor statements. | TWIPLA’s analytics behavior is independently verifiable using standard browser developer tools. |
| 5. | Privacy safeguards must be applied in a way that prevents silent circumvention. | GDPR Art. 25 Privacy by design and by default; GDPR Art. 5(1)(a) Lawfulness and fairness | Test behavior across different modules and configurations to identify inconsistencies, bypasses, or alternative mechanisms that undermine stated safeguards. Positive result: Safeguards remain effective across modules and configurations, and no bypass behavior is observed. Negative result: Safeguards can be circumvented through feature differences, configuration changes, or alternative mechanisms. | TWIPLA enforces privacy controls consistently across all analytics modules, preventing circumvention through feature or configuration differences. |
| 6. | Changes to privacy-relevant configuration must have a measurable effect on processing behavior. | GDPR Art. 25 Privacy by design | Modify privacy settings and observe whether processing behavior changes accordingly. Positive result: Observable processing behavior changes in line with the configuration change. Negative result: Configuration changes do not produce measurable differences in processing behavior, or changes are inconsistent with the expected effect. | TWIPLA’s privacy and tracking modes result in observable and measurable changes in data collection behavior. |
| 7. | Compliance measures must be capable of being assessed over time. | GDPR Art. 24 Responsibility of the controller; GDPR Art. 5(2) Accountability | Review the availability of documentation, configuration history, and evidence supporting ongoing compliance. Positive result: Documentation and evidence, such as configurations and records, exist to support periodic reassessment of compliance over time. Negative result: Evidence is missing or insufficient to support ongoing assessment and accountability. | TWIPLA enables ongoing compliance assessment through documented processing practices, configuration controls, and retained evidence over time. |
Reference Documentation
→ Using browser developer tools to verify network behavior (Chrome DevTools docs)
→ Inspecting request headers and payloads in DevTools (Chrome DevTools docs)
→ Understanding how configuration changes affect requests (Chrome DevTools docs)
→ Verifying data flows through observable system behavior (Chrome DevTools docs)
→ Example of verifiable analytics configuration behavior (TWIPLA documentation)
Review Accountability and Ongoing Compliance
Completion of this framework does not, in itself, establish GDPR or ePrivacy compliance. Compliance depends on how a website integration is configured, operated, and reviewed over time, and remains the responsibility of the data controller.
Changes to product features, configuration, infrastructure, regulatory interpretation, or organisational use can materially affect compliance outcomes. For this reason, verification should be repeated whenever relevant conditions change and incorporated into ongoing governance and risk management processes.
The purpose of this framework is to support informed, evidence-based decision-making by enabling compliance claims to be tested against observable behavior. Where discrepancies arise between documentation, configuration, and system behavior, those discrepancies should be treated as compliance risks requiring review and remediation.

